Tenable Vulnerability Scanner Quick-Start
Section outline
-
Welcome to the Tenable Vulnerability Scanner Quick-Start course.
Tenable Nessus is the authenticated vulnerability scanner used by USM Anywhere.
This quick-start guide shows how to quickly deploy a tenable scanner to perform scans of your assets
This should take approximately 5 minutes to complete.
Notice: These training documents are protected by the United States copyright laws and are proprietary to LevelBlue Intellectual Property. Sale, disclosure, copying, recording, reproduction, merger, translation, modification, enhancement, or use by anyone other than authorized individuals without the prior written consent of LevelBlue Intellectual Property is strictly prohibited.
©2026 LevelBlue Intellectual Property. LevelBlue logo, and registered trademarks and service marks of LevelBlue Intellectual Property and/or LevelBlue affiliated companies. All other marks are the property of their respective owners.
-
-
Tenable Nessus is the authenticated vulnerability scanner used by USM Anywhere.
This quick-start guide teaches you how to quickly deploy a tenable scanner to perform scans of your assets. It also shows how to automatically link the scanner to your new Tenable cloud account, and by association USM Anywhere, during the scanner deployment.
Note: There are many ways to deploy a scanner. Scanners come in multiple formats. For a list of install options please visit the Nessus documentation. Pre-built images may also exist for your cloud or virtualization software. When using these methods you may need to manually link your scanner to your cloud account.
After following the steps in this quick-start guide you will have deployed and configured the following.
-
-
-
This video shows how to quickly set up Tenable in USM Anywhere. The guide underneath contains the steps in this video, as well as links to other deployment methods.
-
-
Step-by-step instructions for enabling and configuring the LevelBlue Vulnerability Scanner powered by Tenable.
Each section contains a time stamp corresponding to the video above.
-
Configure and Enable Tenable
[00:00 - 00:53]
These steps allow you to create credentials and log in to Tenable cloud account. Following these steps will also connect your USM Anywhere sensor to the tenable cloud.
- Navigate to Data Sources and open the Available BlueApps tab.
- Search for Tenable, and then select LevelBlue Vulnerability Scanner Powered by Tenable.
- Click Configure API.
- Enter the email address that will receive the Tenable cloud login credentials.
- Note: This email will not be the email you use to log into the Tenable cloud. The username and password for the Tenable cloud will be auto-generated.
- Select the region where the tenable data will be stored.
- Click Save.
- This will send the credentials to the email address specified.
- This will connect your sensor to your new Tenable Cloud account.
- Once the configuration is complete, you will receive an email confirmation
- Note: If you do not you can choose Actions tab and run the Resend Confirmation Email action. The history tab will show if the resend was successful.
- Open the email and use the credentials supplied to log into the Tenable Cloud.
-
View Cloud Scanners
[00:54 - 01:16]
These steps show how to view the pre-deployed cloud scanners that can be used to scan public facing assets.
- Log into the Tenable Cloud
- Under Your Tenable Products you can open Vulnerability Management
- Note: The Tenable Cloud has the capability to perform other security scans. These are displayed under Enhance Your Security Program. The license provided by LevelBlue doesn’t not include these products.
- Open Vulnerability Management
- Click on Tools > Manage Sensors
- Note: This does not refer to USM Anywhere sensors. It refers to Nessus vulnerability scanners.
- Under Cloud Scanners you can see a list of available cloud scanner. These can be used to scan public facing assets. You will have to allow the cloud scanner IPs connect to your public asset over SSH or SMB/WinRM.
-
Deploy a Local Scanner
[01:16 - 02:00]
These steps are the quickest method for deploying a local scanner.
- Click on Linked Scanners > Add Nessus Scanners.
- Copy the installer script for your operating system.
- Note: The API key to link scanner you’re going to deploy to your cloud account is embedded in the script. An alternative method is to deploy the scanner, or a pre-built virtual machine, and link it manually afterwards.
- Ensure your chose machine meets the system requirements.
- Run the copied command in your chosen operating system.
- At the end of the command you may see instructions for logging onto the local scanners web interface. This isn’t required, however if you would like to create a user to login you may do so.
- Return to the Tenable Cloud and verify that the new, local scanner is visible
-
Download Latest Vulnerability Plugins
[02:00 - 02:20]
These steps show how to download the latest vulnerability plugins for the Nessus scanner. Typically these are downloaded on a schedule.
- Click on Linked Scanners.
- Click on your new scanner, typically called scanner-name.
- Click More > Update Plugins.
- This typically takes a few minutes.
- You can see the current Plugin set, and when it was last updated under Plugins.
- Note: You may change the scanner name to something more useful by clicking on the pencil icon beside the name.
-
Choosing the Scanner in USM Anywhere
[02:20 - 02:38]
These steps show how to choose a default scan type and scanner in USM Anywhere.
- Returning to USM Anywhere open the LevelBlue Vulnerability Scanner Powered by Tenable Advanced BlueApp.
- Select the Scanner Settings tab.
- Choose the Scan Type from the drop-down.
- In the video the Basic Network Scan is chosen. This performs a full system scan that is suitable for any host. Use this to scan an asset or assets with all of Nessus's plugins enabled.
- Choose the local scanner you’ve deployed from the Scanner drop-down.
-
Launching an Authenticated Vulnerability Scan from USM Anywhere
[02:38 - 04:00]
These steps show how to assign credentials and launch a scan.
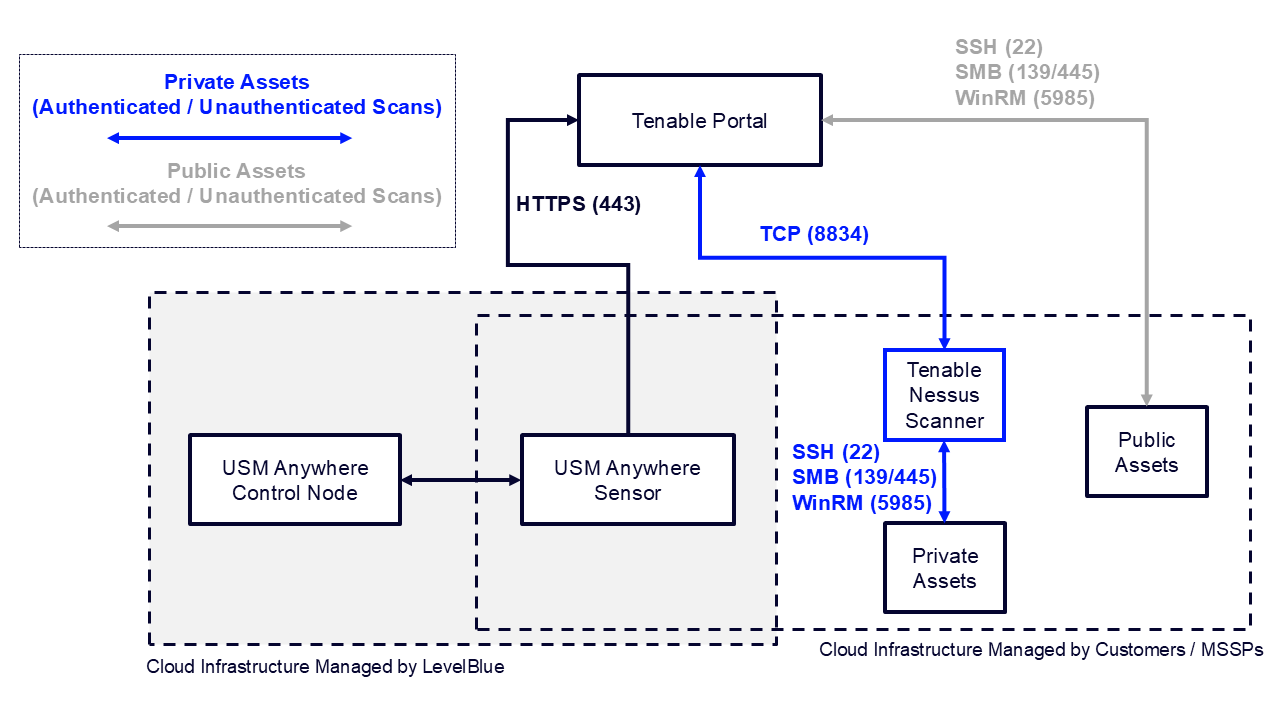
- The local scanner you deployed needs to be able to access certain ports on your assets, such as SSH (22), SMB (139/445) or WinRM (5985), in order to successfully perform an authenticated scan.
- For Unix based operating systems, such as Linux and Mac, the Secure Shell (SSH) service needs to be configured and running.
- For Windows operating systems Server Message Block (SMB) or Windows Remote Management (WinRM) need to be configured and running.
- Create and assign credentials to the asset or asset group you want to scan.
- Open the asset or asset group you want to scan.
- Select Actions > Authenticated Scan to start the scan.
- You can view the progress of the scan in the Scan History tab.
- Once complete you can view the detected vulnerabilities.
-
-
If you would like a provide feedback on the material or the platform, please complete our Survey.
If you would like a certificate for your records, please select the Download Certificate icon. The option will not become available until you have completed all modules of the training course.
